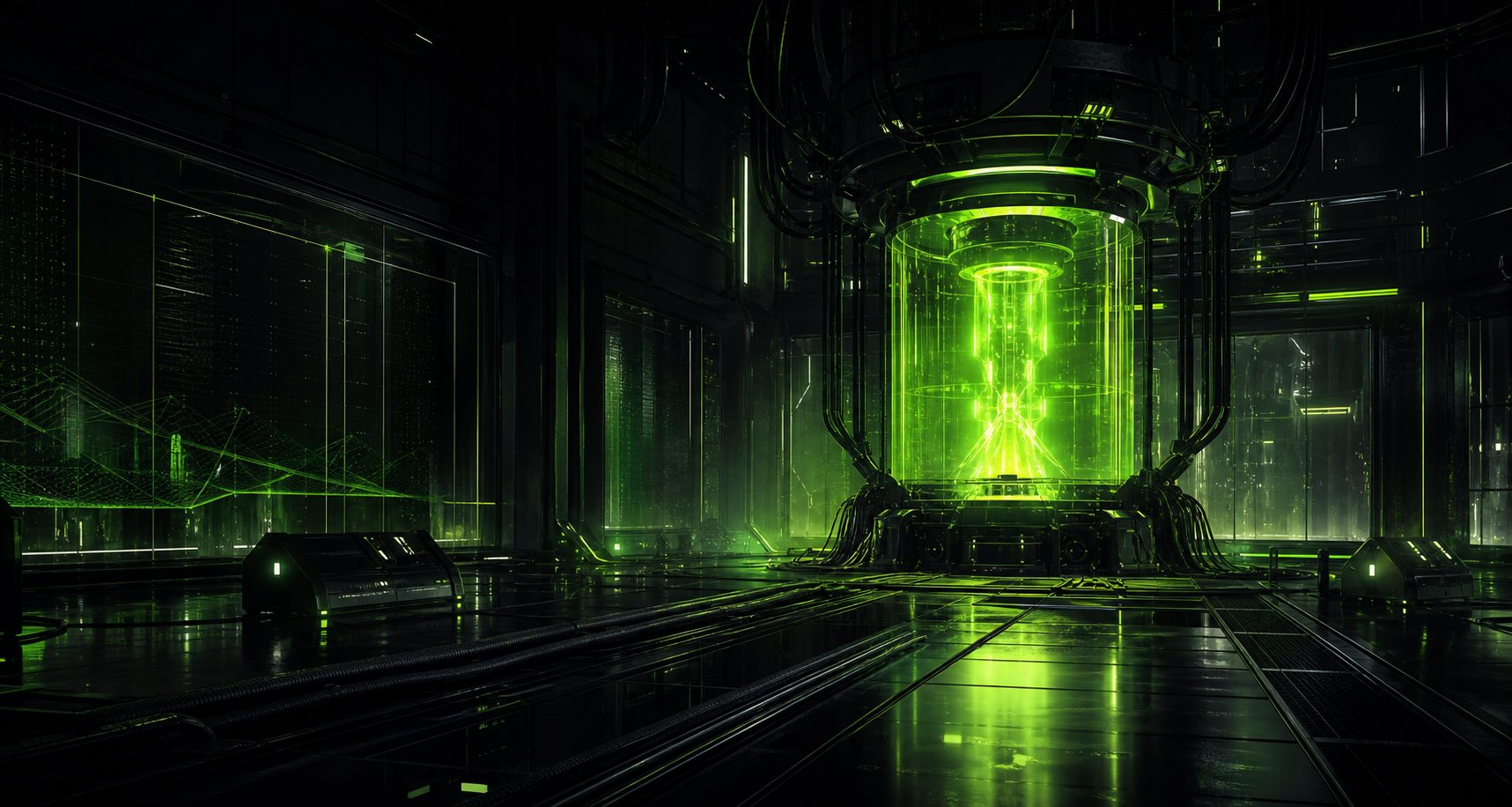
Agentic Automation
Coordinate multi-step AI workflows with operator oversight, deliberate scope, and repeatable execution paths.
Independent AI software project
Activate The Machine
A premium AI automation and agentic software framework for builders who need controlled execution, auditable logic, and operator-grade command over machine workflows.

What it is
Frankenstein Protocol™ is positioned as a premium automation layer for agentic software: a place to define what machines may do, how they are observed, and when a human operator must step in.
Core modules
Each module is designed around narrow access, clear state, and usable controls instead of black-box automation theater.
Coordinate multi-step AI workflows with operator oversight, deliberate scope, and repeatable execution paths.
Design automation surfaces around isolated environments, minimal access, and infrastructure that can be inspected.
Define task rules, escalation points, constraints, and execution boundaries before the machine starts moving.
Track active runs, intervention points, and state changes through a command surface built for human supervision.
Give builders practical primitives for connecting agents, tools, prompts, policies, and deployment workflows.
Record decisions, tool calls, permission grants, and run metadata so activity can be reviewed after execution.
Security first
The protocol philosophy favors local-first design where applicable, no unnecessary access, user-controlled permissions, auditability, transparency, and decisive stop controls.
Roadmap
The early roadmap is intentionally focused: establish the brand, validate the protocol privately, then release developer tools only when the operating model is hardened.
Waitlist
Join the early operator list for updates on the private beta, developer tools, and protocol release milestones.